
Have you ever tried to remember one of the numerous passwords you’ve created for the apps you deploy personally but couldn’t? How much time and nerves did it take? Now let’s imagine an average company with a huge number of staff members and dozens of SaaS applications they use every day.
According to the security protocols, they should authorize the apps on a daily basis and log out of them at the end of every workday. Moreover, each password should be unique to provide the safety of the company’s sensitive data. So, how productive and fast employees work will be if they try to recall every single password approximately every 300 days of the year?
Fortunately, there are services that solve this problem. They help users to log in to the various services integrated with one another, using one credential. This practice is called single sign-on or SSO.
This technology facilitates not only workers’ life. From the employers’ perspective, SSO is also an efficient tool for optimizing business processes like onboarding and offboarding. Company owners don’t need to assign a whole set of credentials for a new worker and then, if leaving, take them back. With a Single Sign-on implemented in the organization, it’s only one login needed.
In this article, we discover what SSO is, how it works, what advantages it can offer, and how you can optimize the usage and costs of SSO services in your company.
What is single sign-on (SSO)?
Single sign-on is an authentication scheme that allows users to access all the deployed SaaS applications, by entering their credentials (username, email, password, and so on) once. SSO combines several services’ login screens into one, which facilitates the authorization process and saves time.
SSO is broadly used in organizations of all sizes, where licenses are assigned and managed by an internal IT Department. Additionally, remote workers benefit from SSO, too, as they log into the services fastly and easily from their personal computers.
Instead of confirming their identity over and over again, an employee does it once and then can access all the needed applications, integrated with the SSO service. It’s also worth mentioning that user identity verification is essential for realizing which permissions each user should have.
How an SSO login work
Every time a user signs in to an SSO service, this service creates an authentication token that identifies the user and remembers that the user is verified.
An authentication token is a piece of digital information (like a user’s credential or the information about the system sending a token) that is stored either within the SSO service or the user’s browser. Simply put, it’s like a user’s ID card.
While using any app, the user gets access to it due to the SSO service initially checking the authentication token assigned to him/her and only then confirming the access. In the case when the user isn’t signed in yet, he will be redirected to the SSO service and access the application through it.
It’s important to mention that the SSO service doesn’t store the user’s identity information, so it doesn’t necessarily remember who the user actually is. In the majority of SSO services, user credentials are checked against a separate identity management service.
So, in other words, SSO is a go-between that can verify whether a user’s credentials match with their identity in the database or not. However, SSO services don’t manage the database themselves.
How SSO authentication tokens work
The most crucial part of the SSO process is its ability to transfer an authentication token to external services and applications. Identity verification that takes place apart from the other cloud services makes SSO possible.
Imagine a party only the privileged individuals have access to. At the entrance, they get a stamp that allows the guards to indicate the approved guests. These stamps have an exact color and shape that is used at this party only, so the guard staff knows that these guests are allowed to be there for sure.
Similar to the stamps, authentication tokens have their own communication standards to ensure that they are correct and legitimate. If the webpages are written in HTML, authentication tokens are written in SAML – Security Assertion Markup Language, which is the main authentication token standard.
Security benefits of Single Sign-On
The simplicity is not the most outstanding advantage of SSO. The most remarkable one is that this solution provides stronger security. This statement may be rather confusing, SSO implies single signing in with the use of one password instead of many different passwords and numerous sign-on operations.
Here you can see several reasons proving that the SSO services deployment is more secure and provides better productivity among employees:
Stronger passwords
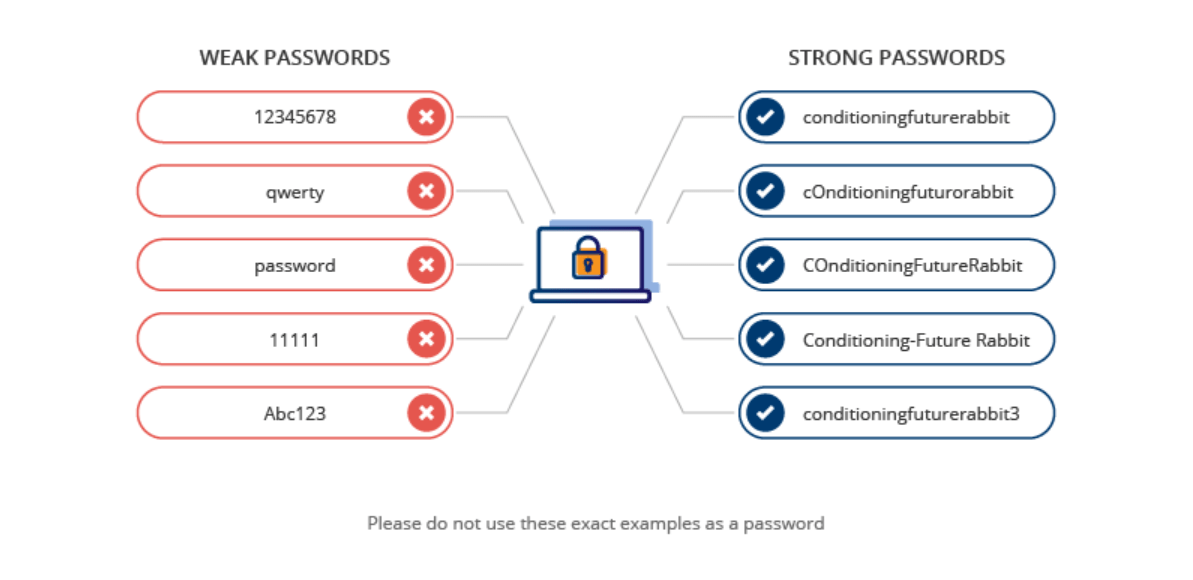
Many users don’t even think about how strong their passwords are. A password can be considered strong and reliable if it’s not easily guessed and consists of numbers, letters (both lowercase and uppercase), and additional symbols like exclamation marks or a dollar sign.
For instance, the h9$ML@85!2 password is assumed to be strong, while password12345 or just 123123 is not.
In theory, SSO encourages users to create a stronger password, as they need to remember and use only one, and it should be reliable.
No reused passwords
It’s nearly impossible to remember all the passwords for several independent apps. That’s why a “password chaos” condition is likely to happen: users will use one and the same password repeatedly across numerous services.
That is a great security risk as if one service’s password database is compromised, cyberattackers can use the password to hack all of the user’s other apps as well. SSO solves this issue by allowing users to authorize with only one login.
Password policy improvement
With SSO, it’s easier for IT teams to implement password security rules and policies. For instance, there are some organizations that ask employees to reset their passwords periodically. SSO facilitates this process, as instead of the constant password reset across a number of different apps and services, workers only have to do it once.
Multi-factor authentication
Even a strong password is not the key to solid security. As someone may obtain your password, and use your credentials to access the data, SSO creates a convenient experience through strong authentication.
Multi-factor authentication, or MFA, is the strongest one. It implies the use of a couple of identity factors to authenticate a user. The first is the possession of credentials – an employee needs to enter the email address and password.
Additionally, the possession of some physical object is considered to be the second factor. For example, when the credentials are entered, a worker should also enter a code sent to his smartphone or email, as well.
SSO makes it possible to activate and start deploying MFA in a blink of an eye, instead of spending time on activating it for several dozen applications.
Internal credential management
It’s a common practice when users store their passwords using some services and applications that may fail in following the best security practices and providing reliable cyberattack protection. SSO, on the other hand, stores all the credentials internally, which grants your IT department more control over their usage and safety.
Faster password recovery
In addition to the above-mentioned security benefits, with SSO, the IT team spends less time on users’ passwords recovery or resetting their passwords for numerous services. Users, in turn, spend less time signing into various apps to continue working on the projects. This SSO peculiarity can potentially increase the productivity of employees working in the company, as well as the business productivity in general.
All in all, using SSO services is advantageous for companies for a variety of reasons but there is still no limit to perfection. Besides the security and convenience aspects, SSO services can be also beneficial in terms of savings.
How to optimize SSO solutions costs
Cloud management platform Binadox has integrations with the following SSO services: Okta, Auth0 (currently part of Okta), and OneLogin. It means that Binadox users can monitor these SSO tools’ utilization rates and manage their costs – SaaS Utilization Dashboard helps to easily perform these tasks.
Additionally, in the SaaS Connections sections, Binadox users can see all the services you authorize through SSO systems (if integrated with Binadox). They will be marked as Discovered and can be connected to Binadox as well to start optimizing them, too.
License manager can be used for these purposes, as it helps users to manage the licenses deployed in the company. It has several tabs: Renewals Calendar, displaying the apps’ next billing dates; Unassigned Licenses, allowing to view the less utilized apps, as well as the potential savings; and Invoices, which facilitates the creation of financial reports.
Try Binadox for free during the 7-day trial period to start optimizing SSO services (and others). Also, you can book a demo to understand how the platform works and how it can help your company in particular.

